What Is a Disposable Email Address? Here’s Everything You Need to Know About It
Privacy has become a top concern in the digital age, and online users often look for ways to keep their identity protected. One example of such privacy-related initiative is the use of disposable email addresses. This post takes a close look at this type of email address and discusses the following points:
- What is a disposable email address?
- Is using a disposable email address illegal?
- What are the types of disposable email addresses?
- What are they used for?
- What risks do disposable email addresses pose?
- How can disposable email addresses be detected?
What Is a Disposable Email Address?
Disposable email addresses (DEA) is an email address that is only used temporarily and can be discarded easily. After a specific amount of time or number of uses, DEAs are most likely disposed of or deleted. For this reason, disposable email addresses are sometimes also referred to as “throwaway email addresses” or “temporary email addresses.”
Types of Disposable Email Addresses
DEAs come in different forms. While they always follow the required syntax where the email prefix and domain are separated by the @ symbol, DEAs could have other purposes. Below are three common types of DEAs, according to how people use them.
- Forwarding email address: Some people give out a different email address but set it up so some or all messages are forwarded to their primary email accounts. This type of DEA is called a “forwarding email address.”
- Alias email address: This type of DEA is also hosted by the user’s primary email service provider. However, they are only used for secondary purposes and their inboxes are seldom opened by the owners.
- Throwaway email address: Throwaway email addresses are created by using a temporary email service. They are primarily for one-time use only, are often created randomly using a variety of characters, and disappear after a certain amount of time.
6 Common Uses of Disposable Email Addresses
As previously mentioned, DEAs are among the technological applications or innovations brought about by the need for privacy protection. Thus, DEAs were initially designed to do just that—protect the privacy of their users. However, some people have also taken advantage of the anonymity and privacy that DEAs provide.
Below are six common ways that people use DEAs. You may notice that they are a combination of positive and somewhat less positive or even malicious applications of the same technology.
- Protect privacy and anonymity: Email addresses are considered personally identifiable information (PII). Giving out your official email address can expose you to the risk of a data breach. To avoid such risks, people resort to using DEAs.
- Avoid marketing emails: Most businesses believe that email is still king and that they can get more sales from email marketing. Others take it further, though, and bombard their target customers with too many marketing emails. To avoid this, consumers have learned to give out DEAs instead.
- Test email workflows: Software and penetration testers use DEAs to test the email workflows of the projects they are working on. That helps them get a sense of the things they need to improve without bombarding their personal or work email accounts with test messages.
- Abuse free trials: Offering freemium features and free trials is a common business model of software-as-a-service (SaaS) companies. The goal is to impress freemium users enough to convert them into paying customers. However, some people abuse this by signing up with multiple DEAs to get away with the limitations of a free account.
- Send malicious messages: The anonymity provided by DEAs can help protect people from getting too many marketing emails, but anonymity also gives some freedom to individuals with nefarious intentions. They may misuse throwaway emails to launch illegal and harmful campaigns, such as delivering malware through emails, for example. This malware would then be a vehicle for threat actors to gain access to victims’ devices.
- Deliver spam: DEAs also provide spammers with the ability to send messages in bulk. And when a disposable email address is blocked due to spamming, they can obtain a new email account almost immediately and continue their campaign.
Is Using Disposable Email Addresses Illegal?
DEAs are not illegal, but how you use them would determine legality. Using them for privacy protection is obviously within your legal rights when no harm is intended. But if you employ them to extort money from people or carry out cyberattacks, you are violating the law.
What Are the Dangers That Disposable Email Addresses Pose?
For businesses, the most apparent effect of DEAs has to do with reduced email marketing campaign performance, particularly increased bounce rates. DEA inboxes could easily reach their storage limits or may not be able to receive messages at all. DEAs could also disappear after a specific amount of time, so any message sent to them would bounce.
There are other repercussions besides email marketing metrics. Failing to reach target customers or freemium users means that there’s little to no chance of converting them into paying customers. Such a situation could be detrimental to businesses, especially those operating on a freemium business model.
Cyber attackers may also use DEAs since those are easy to get and hard to trace. Phishing or malware attacks, for example, could be carried out by using DEAs. The victims would only need to click on a malicious link or download a file for the cyberattack to succeed. And since the victims don’t have to reply to the email, the DEAs can be discarded right after the message is delivered.
What’s more, threat actors can obtain a new disposable email for another attack quite easily. Some providers can immediately give you a temporary email address, which may become unusable after a few minutes or so. There’s no need to fill in a form to open an email account or click on several buttons to delete it.
How to Detect Disposable Email Addresses
Learning what is a disposable email address and how it is commonly used is essential to know if you need to block such emails from your networks. If you find that they pose a danger and should be blocked, the first step would be to detect DEAs.
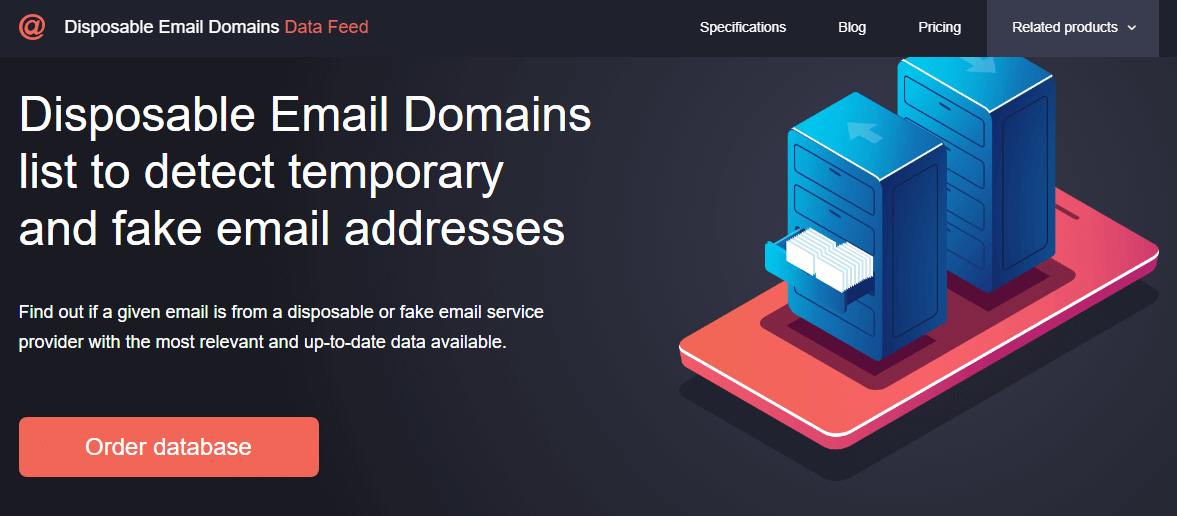
You can do that with the help of Disposable Email Domains Data Feed, a database containing an extensive list of disposable email domains from more than 2,000 disposable service providers. Follow the steps below to detect disposable email domains.
- Get started by leaving a request for the database here. If you already have access, please proceed to the next step.
- Click on the “Order database” button.
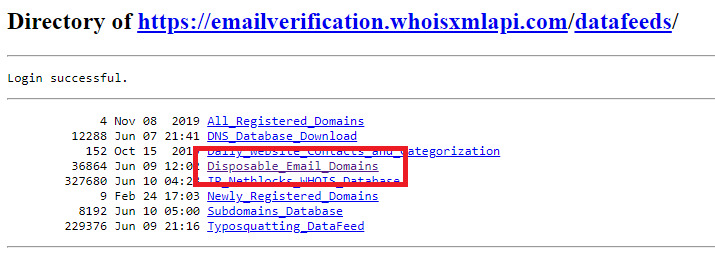
- You will be taken to a page where all the databases you subscribe to are listed. Click on “Disposable Email Domains.”
- The next page displays the daily disposable email domain data feeds. Select the date you want to download. If you want the latest data feed, scroll all the way down.
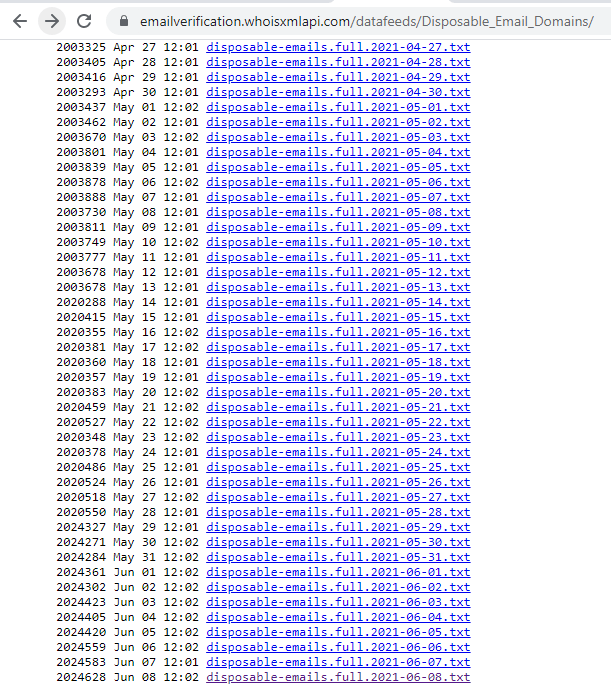
- Click on a specific link to open the .txt file.
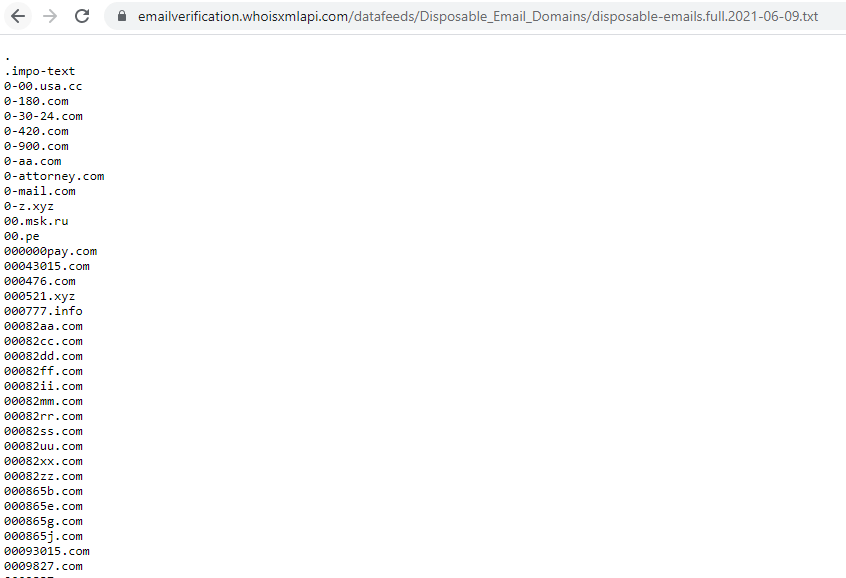
- Search for the email domain you want to verify. If it’s on the file, all email addresses using the domain are disposable.
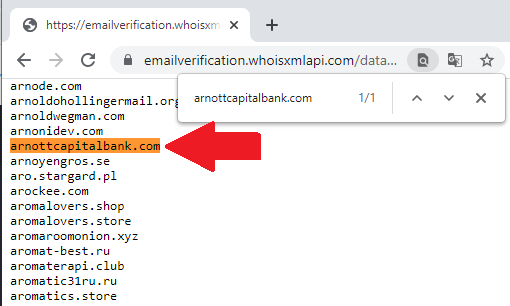
You may copy and paste the data onto a spreadsheet and perform the analysis there. There are more automated ways of using Disposable Email Domains Data Feed to detect disposable emails, depending on the systems you may have. For instance, you can import the data into marketing or cybersecurity tools.
You may also use Email Verification API. Aside from automatically detecting DEAs, the tool can help you detect invalid and nonexistent email addresses.



































